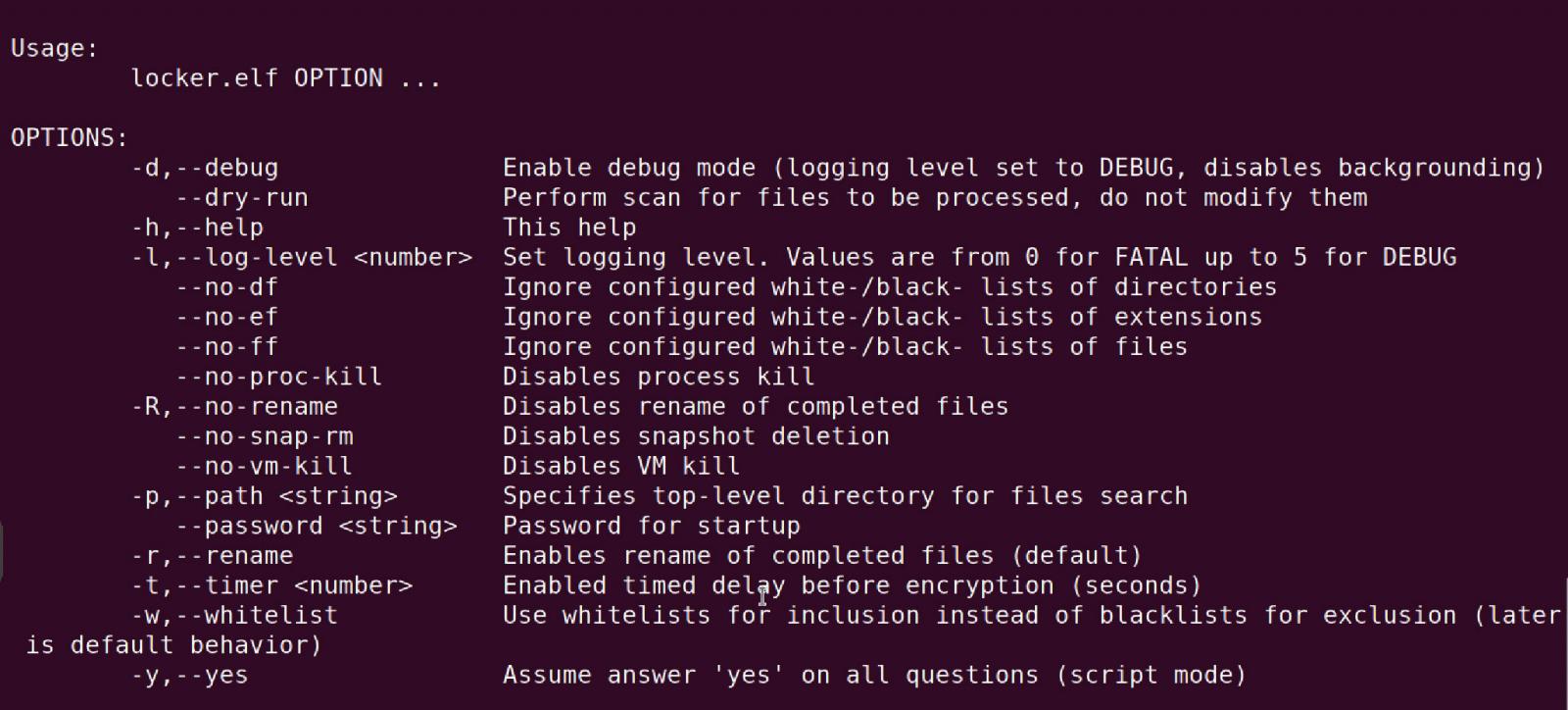
Ransomware Protection For Linux: A Comprehensive Guide
Ransomware has evolved into a significant threat for organizations worldwide, especially for Linux systems. The rapidly changing threat landscape has made it essential to protect your Linux systems from ransomware attacks using the right tools and strategies. In this article, we will guide you through the best practices for ransomware protection for Linux, including the top ransomware protection software for Linux, attack vectors, and prevention strategies.
What is Ransomware Protection Software for Linux?
Ransomware protection software for Linux, also known as anti-ransomware software, is a security solution designed to detect, prevent, and mitigate ransomware attacks that encrypt files and demand payment for their release. The primary function of ransomware protection software is to identify and prevent ransomware threats before they can execute, ensuring that your Linux systems remain secure and your data remains safe.
Halcyon Linux: A Proactive Ransomware Protection Solution
Halcyon Linux is the first endpoint agent specifically built for proactive, real-time ransomware protection tailored to the unique challenges of Linux environments. This innovative solution provides comprehensive defense against ransomware, keeping your most critical systems secure with minimal operational impact. Halcyon Linux is designed to address the unique challenges of Linux environments by providing efficient performance, cross-platform coverage, and robust protection against ransomware attacks.
Top Ransomware Protection Software for Linux
The following is a list of the best ransomware protection software for Linux, designed to provide you with a comprehensive range of options to choose from:
- Halcyon Linux
- Seqrite Anti-Virus for Linux
- Net Protector Total Security for Linux
- ESET HOME Security Premium
- Bitdefender
- Sophos

Attack Vectors and Prevention Strategies
Understanding the attack vectors and prevention strategies is crucial to protecting your Linux systems from ransomware attacks. Some common attack vectors include:
- Phishing emails
- Malware-laden attachments or links
- Vulnerabilities in software
- Unpatched systems
Prevention strategies include:
- Regular software updates
- Implementing a robust backup strategy
- Using a reputable antivirus software
- Limiting user privileges
Conclusion
In conclusion, ransomware protection for Linux is a critical aspect of maintaining the security and integrity of your systems. With the help of the best ransomware protection software for Linux, combined with a solid understanding of ransomware attack vectors and prevention strategies, you can protect your Linux systems from the threat of ransomware attacks. By adopting a layered defense approach, you can safeguard your organization from the devastating effects of a ransomware attack.