Protecting Wi-Fi Network from Insider Threats
The convenience of wireless connectivity has made Wi-Fi networks an essential part of our daily lives. However, this convenience also makes our Wi-Fi networks susceptible to unauthorized access. Insider threats are a significant concern for individuals and organizations, as they can compromise sensitive data and systems. In this article, we will discuss how to protect your Wi-Fi network from insider threats and provide valuable tips on how to prevent such incidents.
Understanding Insider Threats
Insider threats are defined as the threat that an insider will use their authorized access, intentionally or unintentionally, to do harm to the organization's mission, resources, personnel, facilities, information, equipment, networks, or systems. Insider threats can be intentional or accidental and can be caused by employees, contractors, or partners who have access to sensitive data and systems.
Preventing Insider Threats
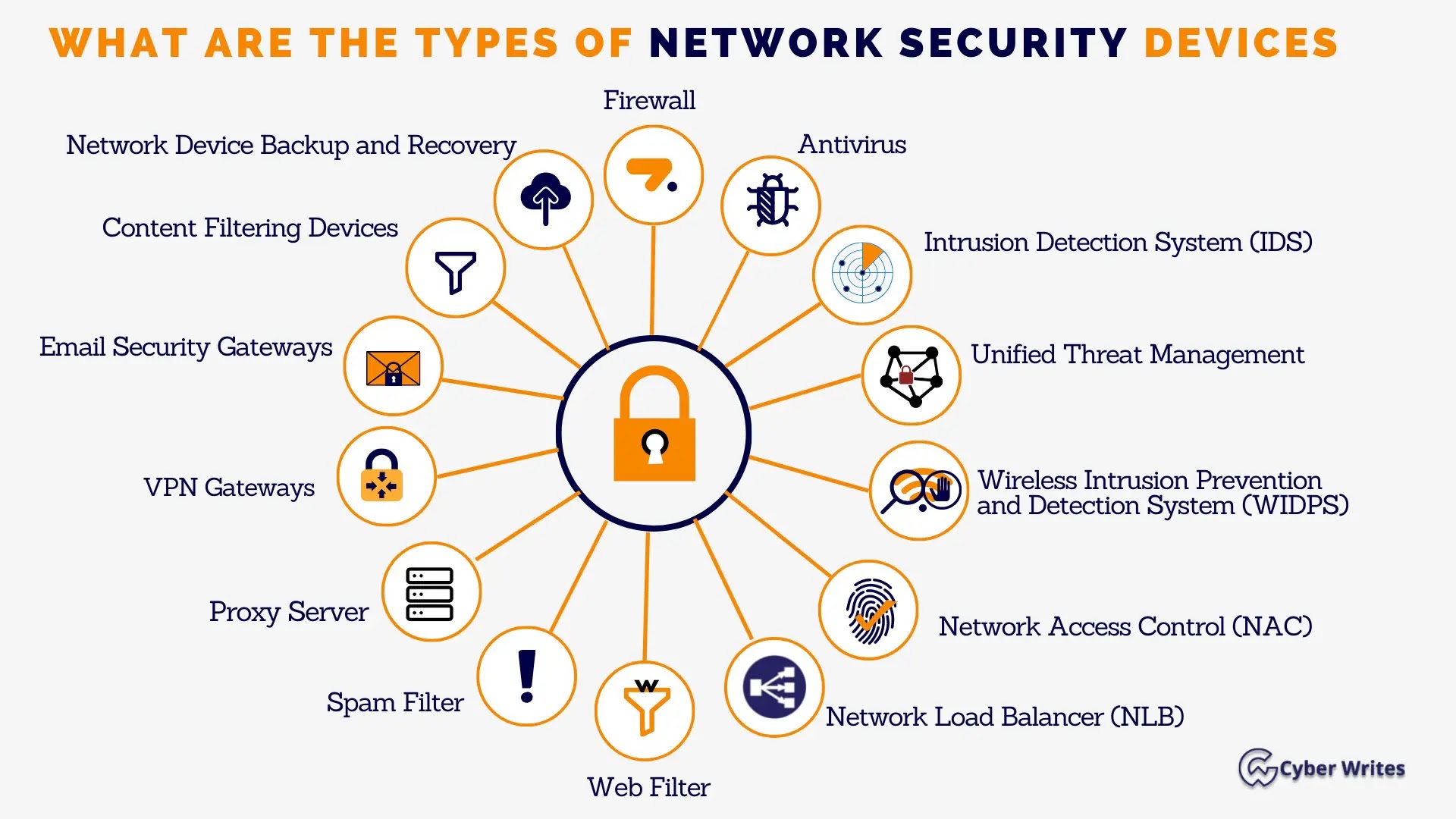
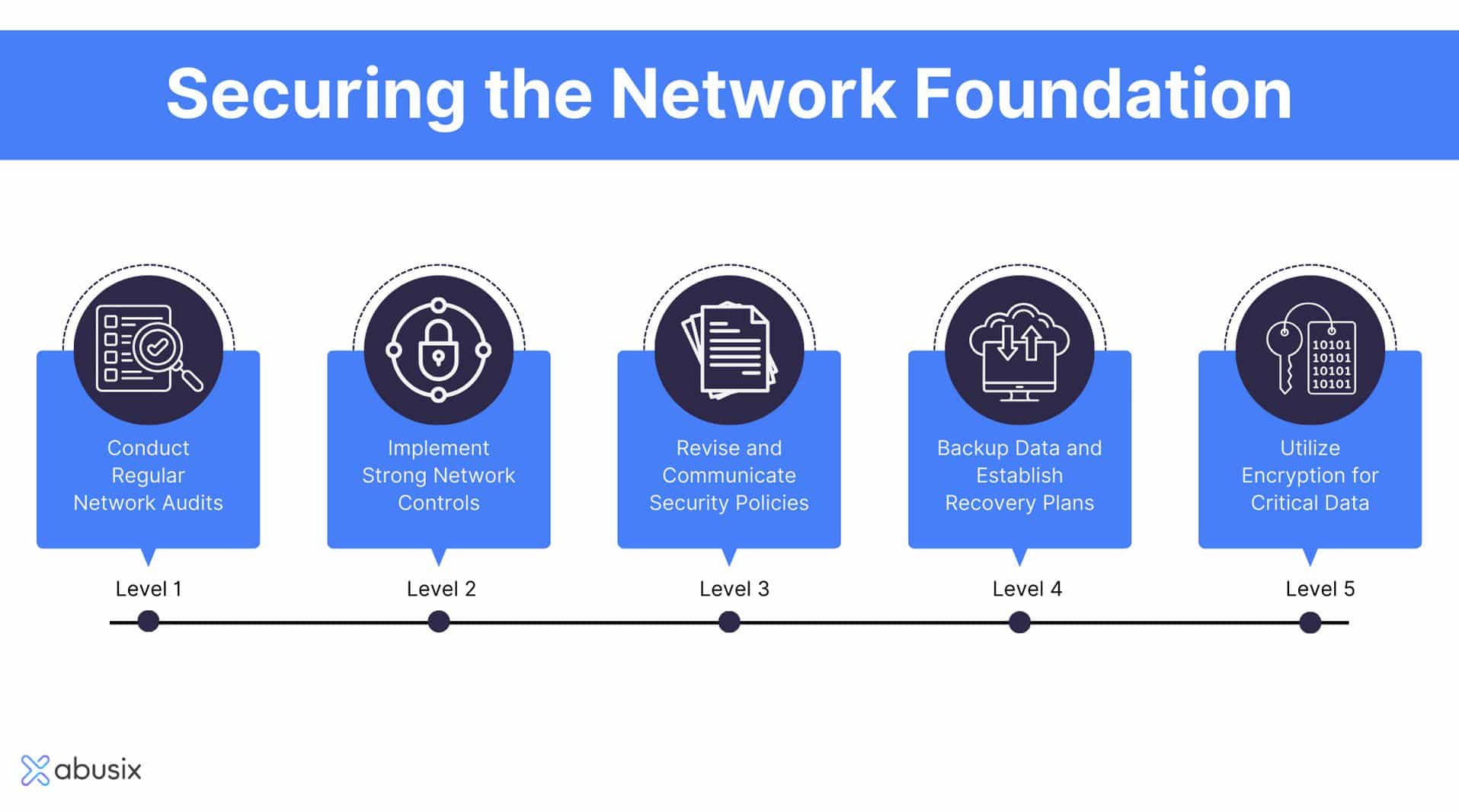
To prevent insider threats, it is essential to implement a layered defense strategy consisting of policies, procedures, and technologies. Some of the best practices for preventing insider threats include:
- Implementing Wi-Fi Protected Access 2 (WPA2) Personal encryption
- Disabling Wi-Fi Protected Setup (WPS) to prevent unauthorized access
- Setting up separate networks for guests to protect the main network from potential threats
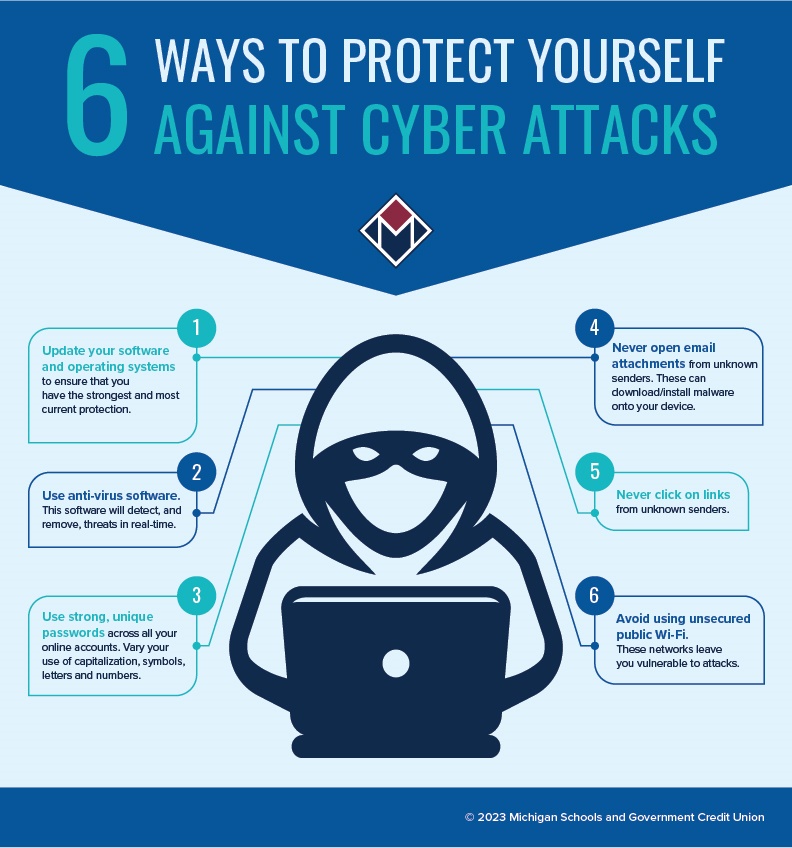
- Educating users about the risks associated with public Wi-Fi and the importance of maintaining strong passwords and avoiding suspicious websites
- Implementing a security information and event management (SIEM) system to monitor and analyze security-related data
- Conducting regular security audits and penetration testing to identify vulnerabilities

Monitoring and Detection
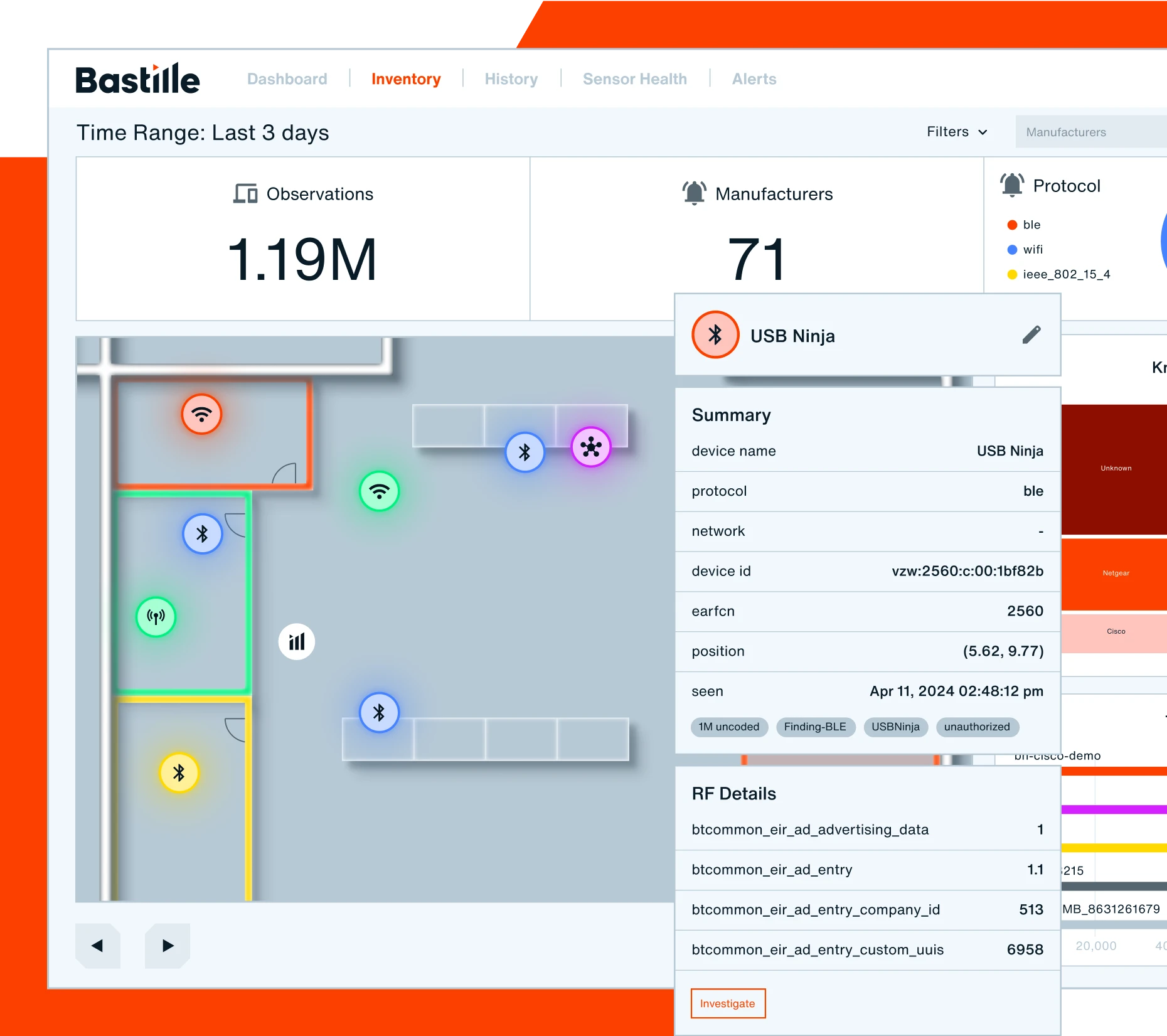
Network monitoring is a crucial aspect of preventing insider threats. It provides security teams with the intelligence needed to detect, investigate, and respond to threats in real-time. Some of the tools used for network monitoring include:
- Wireless intrusion detection systems (WIDS)
- Spectrum monitoring
- Network monitoring software
- Security information and event management (SIEM) systems
Conclusion
Protecting your Wi-Fi network from insider threats requires a proactive approach. By implementing a layered defense strategy, monitoring and detecting suspicious activity, and educating users, you can significantly reduce the risk of insider threats. Remember, insider threats can be intentional or accidental, and they can cost you money and your reputation. Stay ahead of insider threats and safeguard your network security with effective strategies and proactive measures.