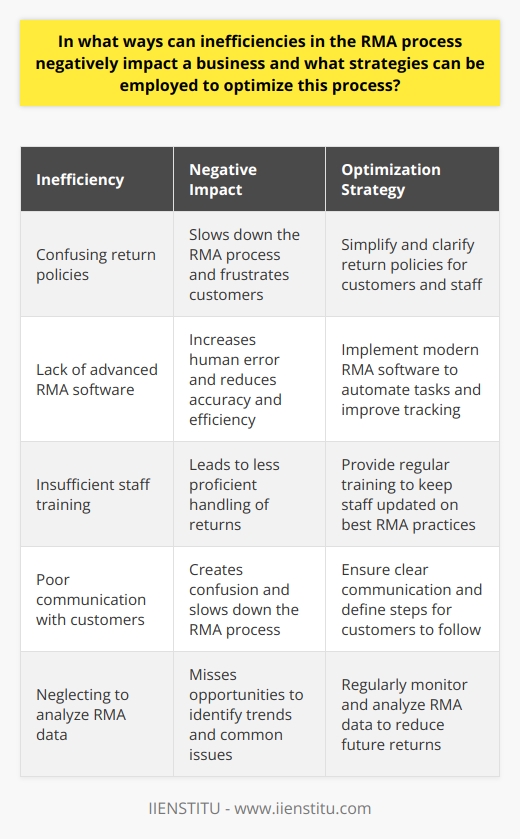
Error-Free Authorization Apparatus Strategy: Enhancing Security in the Digital Age
In today's digital landscape, authorization is a critical component of any robust security strategy. With the increasing sophistication of cyber threats, it's essential to implement an error-free authorization apparatus strategy to safeguard sensitive information and prevent unauthorized access.
Understanding Authorization
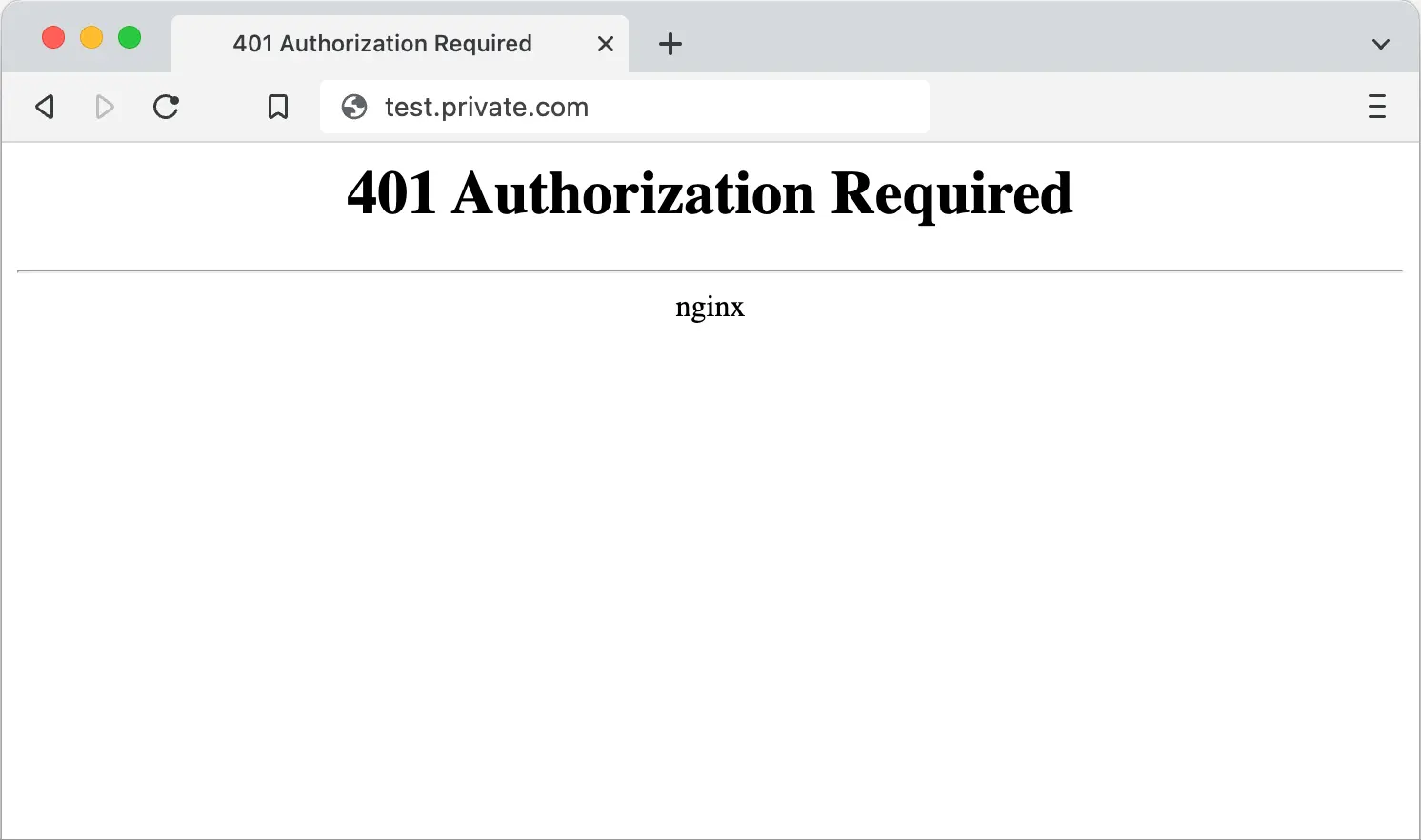
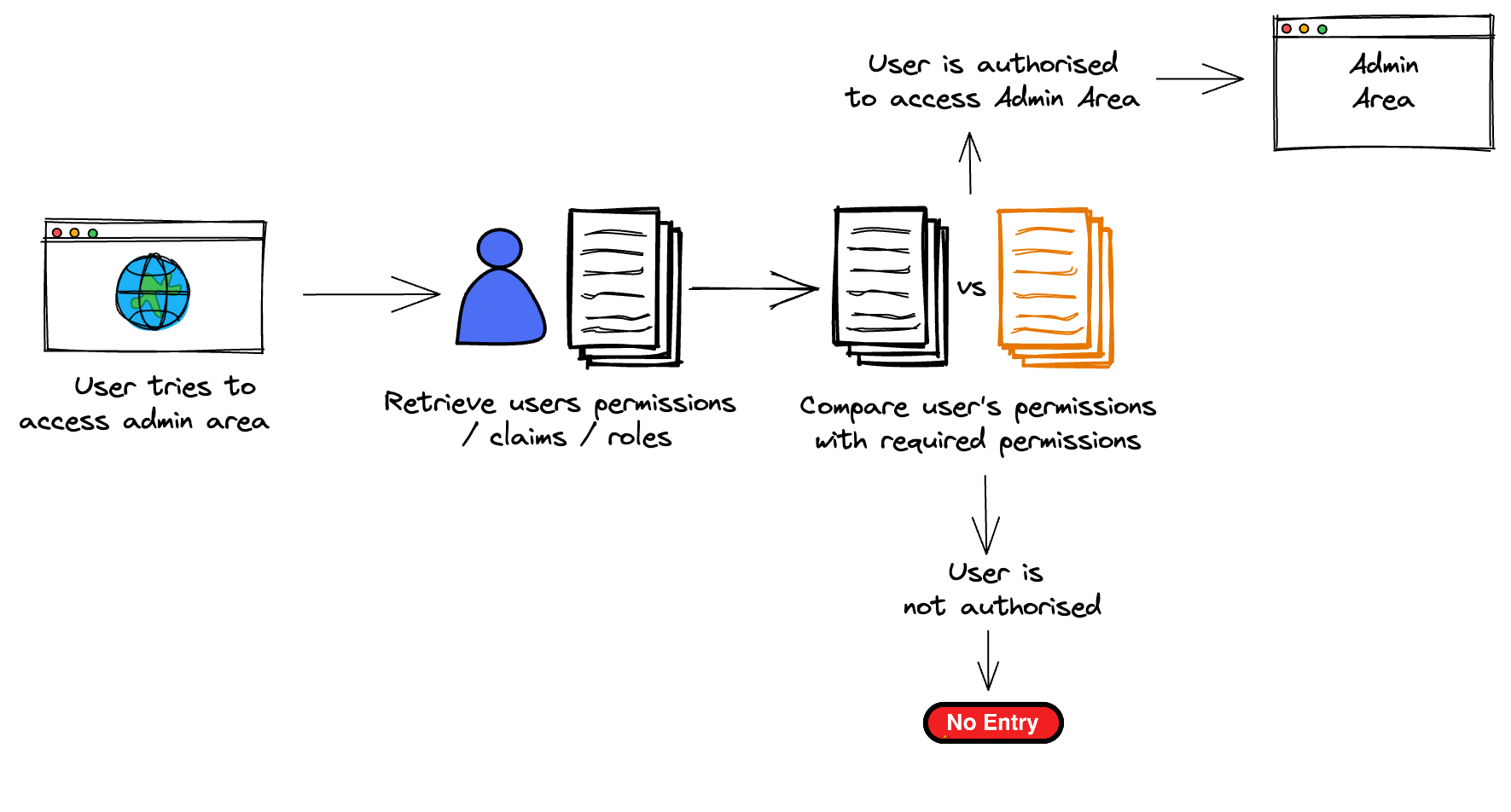
Authorization is the process of verifying that a requested action or service is approved for a specific entity (NIST). It's distinct from authentication, which verifies an entity's identity. When designing and developing a software solution, it's crucial to keep these distinctions in mind to ensure that the correct authorization mechanisms are in place.
The Importance of Error-Free Authorization
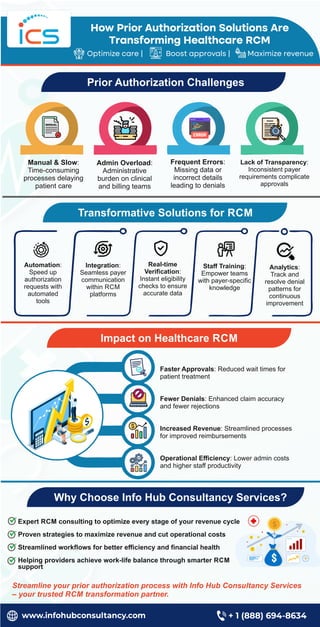
Errors in authorization can have severe consequences, including unauthorized access to sensitive information, data breaches, and even financial losses. An error-free authorization apparatus strategy is essential to prevent these types of incidents and maintain the trust of users and stakeholders.
Key Components of an Error-Free Authorization Apparatus Strategy
- Continuous Monitoring: Regularly monitor security controls and risk-related information to determine if risks remain acceptable over time.
- Centralized Policy Management: Implement a centralized policy management system to streamline access control policies across diverse technological environments.
- Attribute-Based Access Control: Utilize attribute-based access control to ensure that access is granted based on the specific attributes of the user, device, or resource.
- Least Privilege Access: Implement the principle of least privilege access to ensure that users have the minimum level of access required to perform their tasks.
- Auditing and Logging: Maintain robust auditing and logging mechanisms to track and monitor authorization events and detect potential security incidents.
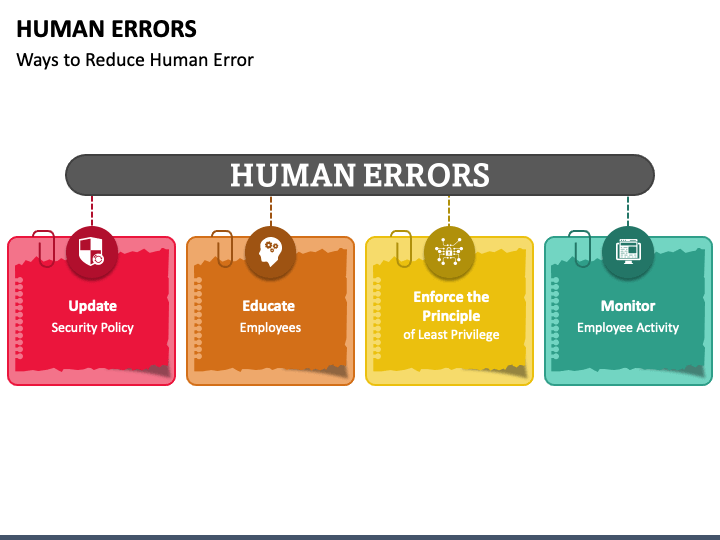
Best Practices for Implementing an Error-Free Authorization Apparatus Strategy
To implement an error-free authorization apparatus strategy, follow these best practices:
- Develop and enforce clear policies and procedures for authorization.
- Implement robust authentication and authorization mechanisms.
- Continuously monitor and assess security controls.
- Regularly review and update access control policies.
- Provide training and awareness programs for users and stakeholders.
Real-World Examples of Error-Free Authorization Apparatus Strategies
Several organizations have successfully implemented error-free authorization apparatus strategies to enhance their security posture:
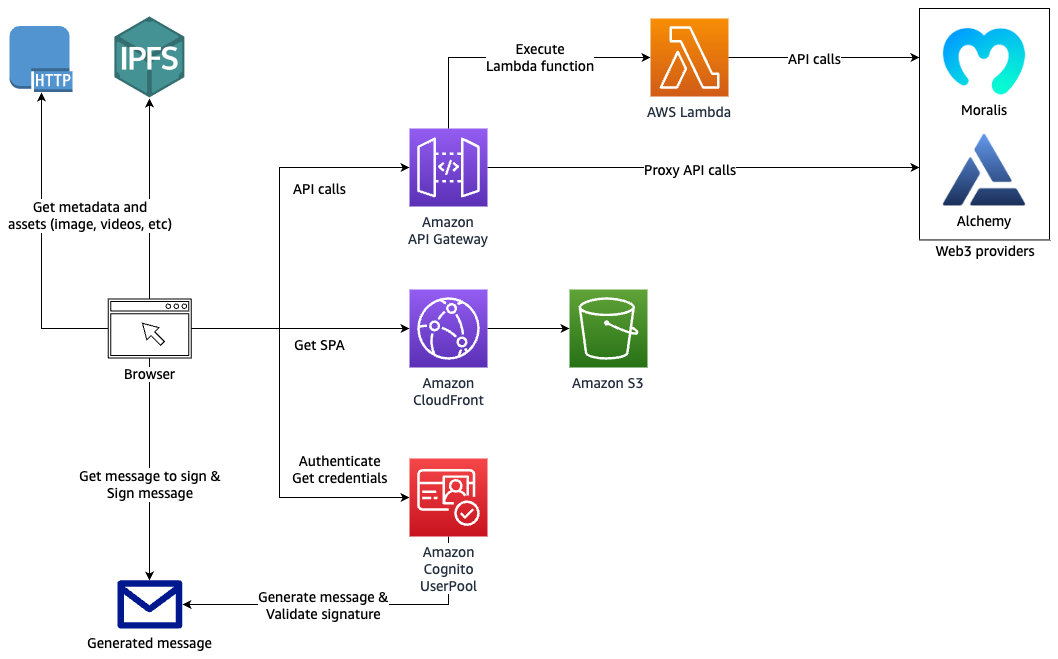
- Microsoft's Azure Active Directory (Azure AD) implements a centralized policy management system to streamline access control policies across diverse technological environments.
- Google's Cloud Identity and Access Management (IAM) service utilizes attribute-based access control to ensure that access is granted based on the specific attributes of the user, device, or resource.
- Airbnb's authorization strategy incorporates the principle of least privilege access to ensure that users have the minimum level of access required to perform their tasks.
Conclusion
In conclusion, an error-free authorization apparatus strategy is essential to maintain the security and integrity of sensitive information in today's digital landscape. By implementing a robust authorization strategy that incorporates key components and best practices, organizations can prevent unauthorized access and minimize the risk of security incidents.