Understanding the Importance of Wireless Network Security Architecture
In today's digital age, wireless networks are an integral part of our daily lives, enabling us to stay connected and productive on the go. However, with the increasing reliance on wireless networks, the need to ensure their security has become paramount. A well-designed wireless network security architecture is essential to protect against various threats and vulnerabilities that can compromise sensitive data and disrupt business operations. In this article, we will delve into the world of wireless network security architecture, exploring its significance, design principles, and best practices.
What is Wireless Network Security Architecture?
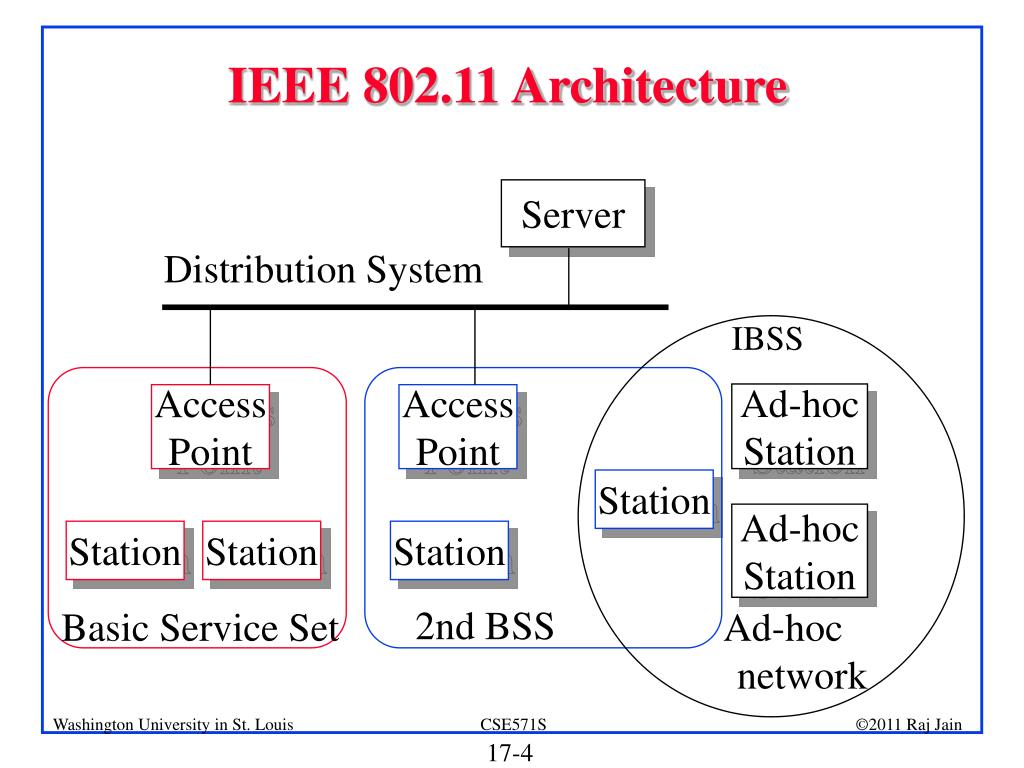
Wireless network security architecture refers to the design and implementation of a secure wireless network infrastructure that protects against unauthorized access, eavesdropping, and other malicious activities. It involves a comprehensive approach to security that encompasses physical, logical, and administrative controls to safeguard wireless networks from a range of threats.
Key Components of Wireless Network Security Architecture
- Authentication and Authorization**: Ensuring only authorized users and devices can access the wireless network, and their activities are logged and monitored.
- Encryption**: Protecting data transmitted over the wireless network using encryption protocols such as WPA3, WPA2, and others.
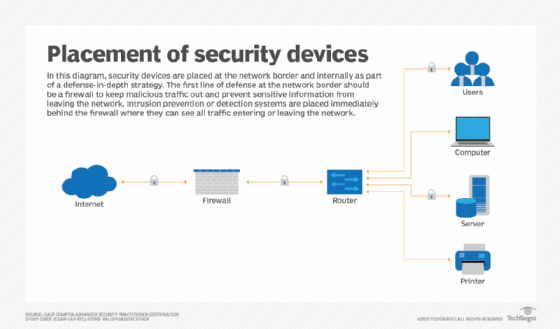
- Firewall**: Implementing a firewall to block unauthorized access to the network and protect against malware and other malicious attacks.
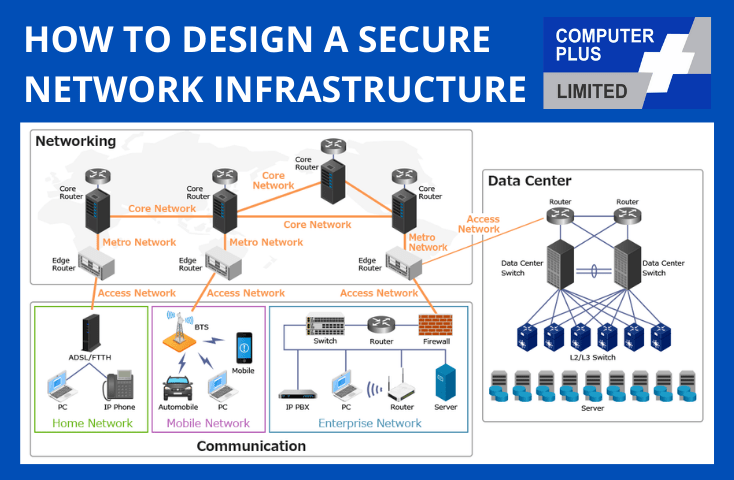
- Network Segmentation**: Isolating sensitive areas of the network to limit the attack surface and prevent lateral movement in case of a breach.
- Wired Equivalent Privacy (WEP)**: Ensuring the security of wireless connections using WEP, a protocol that provides encryption and authentication for wireless networks.
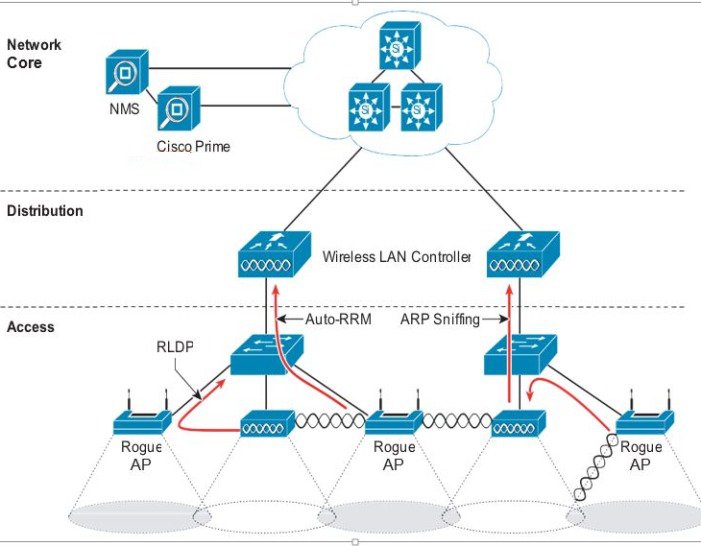
- Wireless Intrusion Detection/Prevention Systems (WIDS/WIPS)**: Monitoring the network for suspicious activity and preventing malicious attacks.
- Regularly updating and patching wireless network and device firmware**: Ensuring all software and firmware are up-to-date to prevent vulnerabilities and exploits.
Designing Secure Wireless Networks
A secure wireless network architecture is built on a solid foundation of security principles, including risk management, threat assessment, and compliance with regulatory requirements. When designing a secure wireless network, consider the following best practices:
- Conduct a thorough risk assessment to identify vulnerabilities and threats.
- Implement a robust authentication and authorization system.
- Use secure protocols and encryption techniques to protect data transmission.
- Regularly update and patch wireless network and device firmware.
- Monitor and analyze network traffic for suspicious activity.
- Implement network segmentation and demilitarization.
Real-World Applications and Case Studies
Wireless network security architecture is not just a theoretical concept; it has real-world applications in various industries. Here are a few case studies:
- NFL's Stadium Network Architecture**: The National Football League (NFL) is implementing a wireless network architecture that includes advanced security features, such as intrusion detection and prevention systems, and network segmentation.
- Industrial Operator Advances Secure, Scalable Wireless Architecture**: A large industrial energy operator has adopted a wireless strategy that supports reliability, predictive maintenance, and digital transformation initiatives while maintaining strict IT/OT separation.
- Verizon Private 5G Network Architecture**: Verizon Business is offering a private 5G network architecture that enables organizations to design a robust infrastructure for their needs.
Conclusion
Wireless network security architecture is a critical component of modern network security. It involves designing and implementing a secure wireless network infrastructure that protects against various threats and vulnerabilities. By understanding the key components of a secure wireless network architecture, designing with security best practices, and applying real-world case studies, organizations can build a robust and secure wireless network that meets their business and security requirements.
References
References cited in this article include articles from industry-leading publications, research papers, and reputable online sources. For further information and resources, consult the cited articles and journals for more in-depth information.
By following the principles and best practices outlined in this article, organizations can ensure a secure and reliable wireless network infrastructure that protects their data and assets.