The Evolution and Integration of UA Enforcement: Ensuring the Safe Use of Participants
Introduction
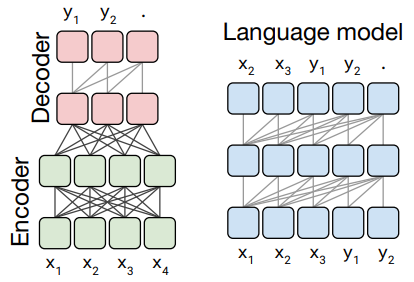
Unmanned Aircraft Systems (UAS) have revolutionized various industries, including aviation, agriculture, and healthcare. As the use of UAS becomes increasingly widespread, the need for robust security measures to ensure the safe use of participants has become more pressing. In this article, we will delve into the importance of safe use of beyond UA encoder participants and explore best practices for mitigating risks associated with UAS operations.A Historical Context: The Emergence of Beyond UA Encoder Use
The advent of Beyond UA encoders has marked a significant milestone in the evolution of UAS technology. These encoders enable the safe and efficient transmission of data between UAS and ground control systems, paving the way for more complex and high-risk operations. As a result, the safe use of beyond UA encoder participants has become a critical aspect of UAS management.Safe Use of Beyond UA Encoder Participants: Challenges and Solutions
The integration of beyond UA encoders poses unique challenges for UAS operators. One of the primary risks is the potential for unauthorized access to sensitive data, compromising the security of the entire UAS system. To mitigate this risk, UAS operators should implement robust encryption methods, such as secure communication protocols and access controls.Implementing Secure Communication Protocols
Implementing secure communication protocols is essential for ensuring the safe use of beyond UA encoder participants. This includes:- Using secure transmission protocols, such as encrypted communication and digital signatures.
- Regularly updating software and firmware to prevent exploitation of known vulnerabilities.
- Implementing intrusion detection systems to identify potential threats in real-time.
Access Controls and Authentication
Access controls and authentication mechanisms are critical components of secure UAS operations. To ensure the safe use of beyond UA encoder participants, UAS operators should:- Implement multi-factor authentication to prevent unauthorized access.
- Use role-based access control to restrict user privileges to specific authorized personnel.
- Regularly review and update access permissions to reflect changes in personnel or job roles.

Regulatory Frameworks and Industry Standards
The safe use of beyond UA encoder participants is also regulated by industry standards and guidelines. The Federal Aviation Administration (FAA) has established guidelines for the safe use of UAS, including requirements for secure communication protocols and access controls.FAA Guidelines and Regulations
The FAA has established regulations and guidelines for the safe use of beyond UA encoder participants, including:- 14 CFR 1.1, which defines a UAS as the UA and its associated elements necessary to support safe flight.
- AC 91-57C, which provides guidance on the safe use of UAS, including requirements for secure communication protocols and access controls.
Conclusion
In conclusion, the safe use of beyond UA encoder participants is a critical aspect of UAS management. By implementing secure communication protocols, access controls, and adhering to regulatory frameworks and industry standards, UAS operators can mitigate risks associated with the integration of beyond UA encoders and ensure secure and efficient operations. As the use of UAS continues to grow, it is essential that UAS operators prioritize the safe use of beyond UA encoder participants to maintain the trust and confidence of the public and regulatory agencies.Recommendations for Safe Use of Beyond UA Encoder Participants
To ensure the safe use of beyond UA encoder participants, we recommend the following best practices:- Regularly update software and firmware to prevent exploitation of known vulnerabilities.
- Implement multi-factor authentication and role-based access control.
- Use secure transmission protocols and digital signatures.
- Conduct regular security audits and risk assessments.